Europe’s progress towards digital sovereignty needs DOING. Urgently. At speed. Not definitions. We need to fund it and build it. Still, measurements are what everyone is coming up with – there are a few out there and more on the way. How do they compare? Do we have too many already? Will we converge onto something, and move quickly to the real job of “doing”?
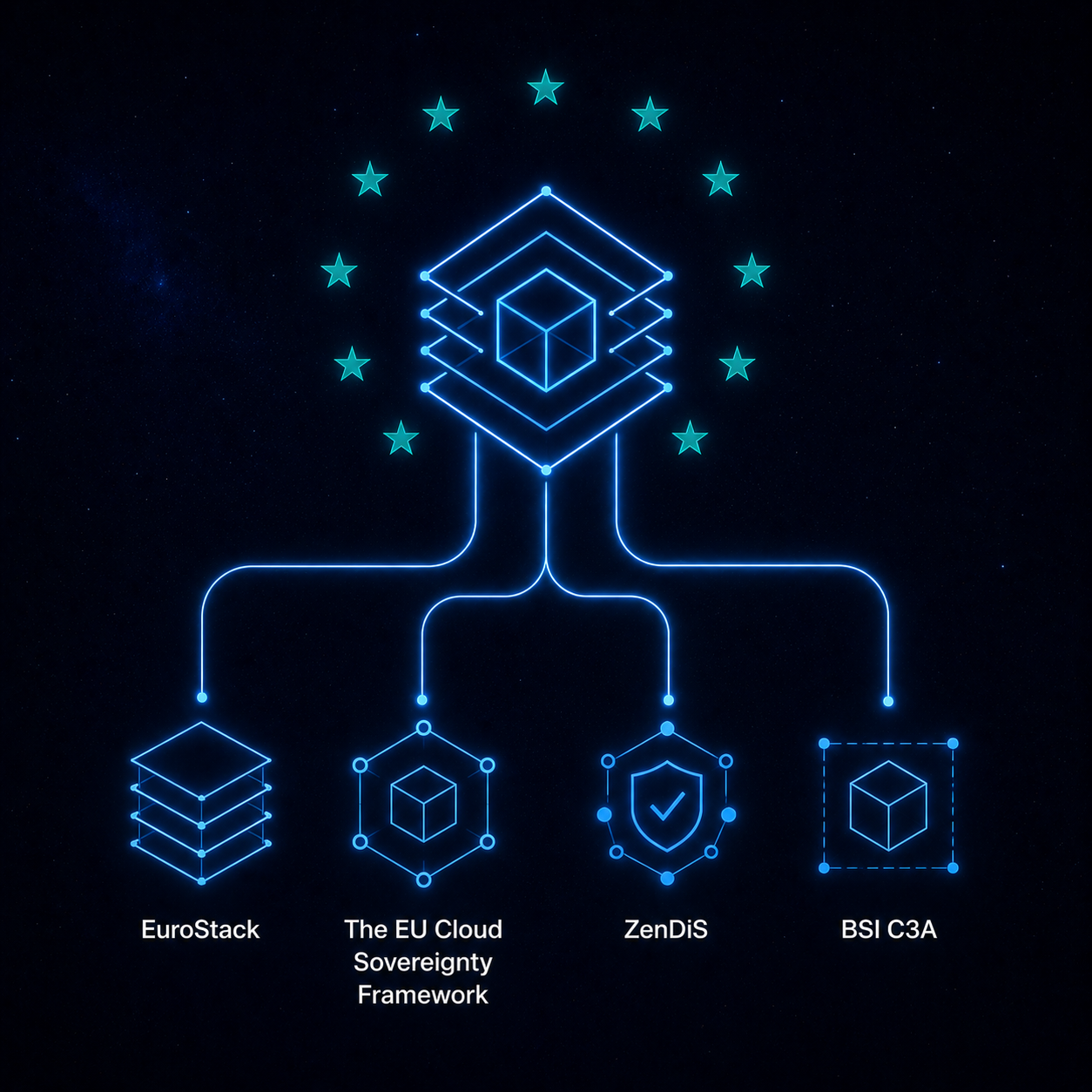
EuroStack was among the very first to put out in September 2025 a proposed set of principles for what should qualify as “European” for purposes of a “Buy European” rule in public procurement (see ourBuy European paper). We articulated a set of cumulative criteria, which we refer to as the JOTED list (Jurisdiction, Operational, Technical, Economic and Data Sovereignty). Then came the European Commission last October with its Cloud Sovereignty Framework (CSF) for its own procurement. The Digital Resilience Index was launched officially in Paris in January 2026. Then we had the proposed European Sovereign Stack Standard (ES³) from Schwarz Digits, the digital arm of Germany’s Schwarz Group, which we commented on already in our bloghere. And more have been coming out: Germany’s Zentrum für Digitale Souveränität (the influential ZenDiS) published its owndiscussion paper on sovereignty criteria in March 2026, currently open for public consultation until 15 May. Then there is also Germany’s BSI C3A framework, issued by the cybersecurity agency. CISPE, the Brussels-based trade association for IaaS cloud providers, launched its Sovereign & Resilient Cloud Services Framework in Brussels at the end of April. And the Commission’s forthcoming CADA (Cloud and AI Development Act) – promised for the end of May – is also expected to contain its own criteria: promised to be an “evolution” of DIGIT’s CSF and intended to create a focal point.
Why so many? Because they approach the same challenge from different angles: different audiences, different purposes. Each framework asks the same fundamental question: how do we know whether our digital infrastructure is truly sovereign? Their answers, however, differ in scope, methodology, and political ambition. But it is also encouraging they converge so much. So while some will try to leverage this multiplicity of frameworks as the usual sign of Europe’s fragmentation and cacophony of voices, it is remarkable there is in fact so much of a common vision.
We start briefly summarising the two earliest benchmarks we already discussed previously: EuroStack and DIGIT’s. We then compare and evaluate Zendis’ and the BSI’s C3A, highlighting points of commonality and departure. We are generally supportive of all approaches, with nuances. Let’s agree and move on.
EuroStack: The Case for a Hard Gate
The EuroStack initiative approached sovereignty through a clear political and economic lens. Where others (like DIGIT’s CSF framework, see below) use various versions of flexible scoring systems, EuroStack proposes a mandatory, more binary pass/fail gate on jurisdictional control. If the ultimate parent entity of a provider is not under EU jurisdiction, that provider should be excluded from strategic procurement – full stop. 50 shades of grey is not something appreciable in terms of digital sovereignty.
This is not in any way protectionism, but what we see as a structural safeguard against “sovereignty-washing”: the practice of non-EU providers marketing tailored offerings as “sovereign” while effectively remaining subject to foreign legal obligations (the CLOUD Act). EuroStack’s framework demands that sovereignty be “cryptographically impossible” to circumvent, that 100% of personnel with privileged access meet strict EU-based criteria, and that more than 50% of a provider’s global R&D expenditure be located in the EU.
Of course, we understand a distinction must be made between short-term and long-term goals. A transition to digitally sovereign systems as quickly as possible naturally also requires flexibility in its operational implementation. Still, we are clear that stopping halfway is a journey without a destination.
The EU Cloud Sovereignty Framework: Scoring Sovereignty on a Ladder
The Commission’s framework of October 2025 defines eight sovereignty objectives: Strategic Sovereignty (SOV-1), Legal & Jurisdictional Sovereignty (SOV-2), Data & AI Sovereignty (SOV-3), Operational Sovereignty (SOV-4), Supply Chain Sovereignty (SOV-5), Technology Sovereignty (SOV-6), Security & Compliance (SOV-7), and Environmental Sustainability (SOV-8). Each objective is graded on a five-level scale, the Sovereignty Effectiveness Assurance Levels (SEALs), ranging from SEAL-0 (no sovereignty) to SEAL-4 (full digital sovereignty). For any given procurement, the contracting authority sets a minimum SEAL level as a mandatory entry requirement. Providers that clear the threshold are then scored competitively using a detailed sovereignty score (SOV) weighted across all eight objectives.
The framework was designed for the Commission’s own procurement, and it has already proven its worth. In April 2026, the Commission awarded its €180 million sovereign cloud tender to four providers: a Post Telecom-led consortium with CleverCloud and OVHcloud, STACKIT, Scaleway, and a Proximus-led consortium partnering with S3NS (a Thales-Google Cloud joint venture), Clarence, and Mistral. Three of the four reached SEAL-3 (“Digital Resilience”), meaning their services are largely immune from non-EU supply chain disruption. The Proximus/S3NS bid, built on Google Cloud technology but operated by EU companies, reached SEAL-2 (“Data Sovereignty”).
This outcome illustrates both the framework’s strength and its most debated vulnerability. The scoring system demonstrably rewards European providers. But the fact that a service built on Google Cloud technology could qualify at all – even at a lower level – is what many found troubling. Still, the award of the tender is a crucial point. The EC is demonstrating that its sovereignty framework is proving its practical viability.
ZenDiS: Sovereignty as an Organisational Health Check
As a prior observation: ZenDiS is currently moving beyond the confines of the German administrative framework – and while the organisation itself remains a public body, its products are being made suitable for a mass market through a European partner network. This makes their proposal of more general relevance than just the German administration.
The ZenDiS criteria are distinctive in their breadth. While the EC and EuroStack focus primarily on cloud services and procurement, ZenDiS assesses sovereignty at the level of the entire public organisation with criteria structured along four categories: Organisation, Applications, Data, and Operations.
The “Organisation” category sets ZenDiS apart, as it asks whether digital sovereignty has been embedded as a strategic objective, whether exit strategies for critical systems have actually been tested, and whether the organisation has the competence and governance structures to exercise meaningful influence over its technology providers. This is deserving and goes beyond what either the EC or EuroStack currently address.
On the technical side, ZenDiS examines whether “applications” are modular, transparent, and interoperable, whether they allow for genuine provider switching (“Wechselmöglichkeit”), and whether the full software supply chain is traceable. For “data”, the criteria cover not just GDPR compliance but also protection from extraterritorial legal access – a direct nod to the risks posed by the US CLOUD Act and several other legal instruments. In “operations”, the focus is on independence of day-to-day IT management, resilience against external disruption, and the ability to maintain services autonomously.
Critically, ZenDiS combines all of these criteria with a risk-based weighting system. Not every IT system needs the same level of sovereignty scrutiny; the criteria are designed to be applied proportionally, depending on data sensitivity and the criticality of a given dependency. The result is intended to be a practical “Souveränitätscheck” – a tool that public authorities at federal, state, and municipal level can use to audit and progressively improve their sovereignty posture.
Let’s compare these three:
Commonalities
Despite their different scopes and methods, these three sovereignty approaches share a remarkable degree of substantive agreement on what sovereignty actually means.
All three identify extraterritorial legal access as a core threat. ZenDiS warns that EU server locations alone do not prevent data access by foreign authorities; the EU framework explicitly scores exposure to non-EU laws; EuroStack treats it as a disqualifying condition.
All three champion open source, open standards, and interoperability as essential foundations. ZenDiS requires transparency of source code and open interfaces for its sovereignty criteria. The EU framework rewards technology built on open licences with audit, modification, and redistribution rights under SOV-6. EuroStack places open source at the centre of its proposed stack.
All three insist on genuine provider switchability. The ZenDiS concept of “Wechselmöglichkeit” maps directly to the EU framework’s portability requirements under SOV-6 and to EuroStack’s criterion of “Operational Reversibility.”
And all three recognise that data sovereignty requires more than localisation – it demands customer-controlled encryption and protection of metadata, backups, and logs, not just primary data stores.
Some divergences
The most consequential divergence concerns the treatment of non-EU providers. The EU framework’s flexible SEAL system permits providers with non-EU parent companies to participate in tenders, provided they reach the minimum threshold and compete on score. The EC clearly wants to avoid going head-to-head with hyperscalers’ (empty but noisy) legal threats they would be “discriminated against” and this would be illegal under EU law. We know this is what ultimately killed Gaia-X, and the EC is thus framing the same goal in terms of attainable levels of “sovereignty” on a gradient. As EuroStack we see the rationale but it is inevitably a structural weakness that enables sovereignty-washing by design. ZenDiS does not take a position on provider origin per se, focusing instead on measuring the outcome – how sovereign is the organisation’s actual posture, regardless of which provider is behind it. Again this is pre-empting a fight but also open to sovereignty washing.
Overall
EuroStack supports both the ZenDiS and EU frameworks as significant advances, though we would like to see three specific refinements.
First, it would be good for the ZenDiS organisational dimension to be integrated into EU- thinking. The Commission’s framework evaluates individual cloud services in isolation; ZenDiS’s insistence on assessing governance, strategy, and institutional capability addresses the reality that sovereignty is not a product feature but an organisational competence. A municipality running the most sovereign cloud in Europe is still vulnerable if it lacks the skills, contracts, and exit strategies to exercise its options. EuroStack’s broader European ambition would benefit enormously from this kind of holistic assessment becoming accepted standard across member states.
Second, we would like to constructively challenge the EC’s SEAL-2 minimum threshold. The takeaway from the April 2026 tender will be for many that a service built on non-EU technology can qualify, even if at a lower score. For strategic public infrastructure, EuroStack’s position is that this is insufficient. For procurement classified as touching “essential security interests,” the minimum threshold be raised to SEAL-3 or SEAL-4, effectively requiring immunity from non-EU supply chain disruption. This would align the EC’s methodology with EuroStack’s policy objectives without requiring the Commission to abandon its scoring approach.
Third, we at EuroStack are concerned about a gap that neither the ZenDiS criteria nor the EC framework adequately address: the economics of sovereignty. Both frameworks assess what sovereignty looks like in technical and legal terms, but neither sufficiently grapples with the market conditions required to sustain it. This is where EuroStack’s call for the state acting as anchor customer and an active challenge of B2B customers to check, try and PoC European services for the sake of European economic wealth. Without active demand on the buyers’ side, even the most rigorous criteria will simply document Europe’s dependency rather than resolve it.
Another one: Germany’s BSI C3A framework
Germany’s BSI C3A framework is a security and resilience benchmark established by a cybersecurity agency. Its main objective is to evaluate technical architectures (gateways, SOCs, SBOMs). That said, it shares multiple objectives with EuroStack and others: establishing rigorous, verifiable criteria for a “Sovereign European Provider” to reduce reliance.
Unsurprisingly given the different audience and purpose, BSI’s C3A and EuroStack emphasise somewhat different mechanisms for procurement, and requirements are structured slightly differently. Still BSI’s 6 pillars map quite closely to EuroStack’s 5 dimensions (JOTED):
- Strategic & Legal (BSI SOV-1 & SOV-2) ↔ Jurisdiction & Governance (EuroStack): Both frameworks require a EU-based headquarter, structural insulation from foreign laws, and effective corporate control by EU entities. EuroStack goes slightly further by defining a strict metric (>50% of ultimate voting rights) and framing it as a Level 1 “Pass/Fail” procurement gate, whereas BSI focuses on assessing extraterritorial exposure, audit rights, and “effective control”.
- Operational (BSI SOV-4) ↔ Operational Sovereignty (EuroStack): Both mandate that infrastructure and control planes be physically located in the EU. Both strictly require EU-resident staff for any roles involving privileged access to infrastructure or customer data (acting as a “human firewall”). BSI further requires a dedicated Security Operations Center (SOC) within the EU.
- Data (BSI SOV-3) ↔ Data Sovereignty (EuroStack): Both require strict data localization. EuroStack explicitly expands this to include all metadata, logs, and backups, while demanding state-of-the-art technical barriers. BSI similarly mandates external key management (where the CSP cannot access the keys), client-side encryption, and strict logging controls.
- Technology (BSI SOV-6) ↔ Technical Sovereignty (EuroStack): Both focus on preventing vendor lock-in and ensuring continuous delivery. However, their approaches differ: EuroStack specifically mandates interoperability via the predominant use of Open Source Software. BSI focuses on technical resilience, mandating a local backup of the source code in the EU that is never older than 24 hours, containing at least 5 versions of the cloud services.
- Supply Chain (BSI SOV-5) ↔ Sub-category of EuroStack’s Operational Sovereignty: BSI carves this out as a distinct 5th pillar, requiring a Software Bill of Materials (SBOM), hardware dependency tracking, and mitigation of export restrictions. EuroStack integrates this under “Criterion 3.3: Supply Chain Resilience”.
- No direct BSI equivalent ↔ Economic Sovereignty (EuroStack): BSI is strictly a technical/security framework and does not measure a provider’s economic footprint. EuroStack treats Economic Sovereignty as a “Key Differentiator” (Level 3 award criteria), requiring the provider to have >50% of its global R&D in Europe, prohibit punitive data egress fees, and actively contribute to the European SME and Open Source ecosystems.
Commonalities
Both BSI and EuroStack exclude standard hyperscalers, making clear that standard cloud offerings from AWS, Microsoft, and Google do not meet true sovereignty standards. EuroStack explicitly labels localized foreign clouds as “sovereignty washing”. while BSI’s strict rules on EU corporate control and external service dependencies effectively filter them out.
Human & Physical Firewalls: Both frameworks insist that mere servers in Europe are not enough; the overarching control plane and the staff managing it must also be exclusively European.
Regulatory Ambition: Both are designed to move beyond abstract policy into actionable benchmarks for public procurement and the forthcoming EU Cloud and AI legislative acts.
Some differences & nuances
BSI has an explicit defense/national security lens: data centers must be able to physically “disconnect” from non-EU networks, maintain operations, and be able to reconnect/install updates after up to 90 days offline. Furthermore, BSI mandates that in a “State of Defense” the CSP must enable the government to completely take over the cloud capabilities. EuroStack doesn’t quite go there, demanding instead “Operational Reversibility” i.e. requiring infrastructure-as-code and comprehensive documentation so a competent third party can completely take over and redeploy the service if the provider fails or is sanctioned.
EuroStack has an Industrial Policy objective, BSI is a Security Standard. Our JOTED framework is conceived as an industrial policy tool, where a key objective is to limit the “extraction of European value” by ensuring European public money funds local builders rather than foreign competitors.
Application in Procurement: EuroStack specifies a legally mapped 3-Level hierarchy for public tenders. Jurisdiction/Legal is a Level 1 strict “Pass/Fail” selection criterion. Technical/Operational/Data are Level 2 “Core Guarantees” (technical specs), and Economic is a Level 3 “Award Criterion” used to break ties and incentivize ecosystem investment. BSI functions instead as a customizable certification baseline (Criteria vs. Additional Criteria) for auditing.
A Framework of Frameworks?
What is happening in Europe is not a single, unified definition of digital sovereignty but an emerging ecosystem of complementary instruments. BSI proceeds from the need to set security standards. ZenDiS provides a diagnostic tool for individual public organisations to understand their own sovereignty posture and identify actionable improvements. The EC Cloud Sovereignty Framework provides one procurement mechanism – a standardised way to demand and score sovereignty in purchasing decisions. EuroStack is about the higher-level strategic vision and will to press on to strengthen European alternatives.
This can be confusing: too many overlapping criteria, too little interoperability between assessment models, and too much room for providers to cherry-pick which framework favours them. But coherence and alignment are possible, with some cross-pollination. If the ZenDiS Souveränitätscheck feeds into EC procurement decisions, if the EU SEAL system is calibrated to reflect EuroStack’s hard-line on effective control for critical infrastructure, and if EuroStack’s ‘Buy European’ agenda creates the market conditions for European providers to actually compete (and more) – Europe would have something genuinely unprecedented: a sovereignty strategy that is measurable, enforceable, and working on market demand.
The consultation on the ZenDiS criteria will close soon (15 May 2026), and remains a concrete opportunity for EuroStack members, European technology companies, and anyone who cares about the integrity of public digital infrastructure to shape what may become the most practical sovereignty tool in Europe’s arsenal. The Commission has demonstrated, with its €180 million tender, that sovereignty criteria can be applied in real procurement. Now the question is whether Europe has the will to set the bar at the right height.
The ZenDiS consultation is open at souveränitätscheck.de. The EC Cloud Sovereignty Framework (v1.2.1) is available on the European Commission’s website. The EuroStack initiative’s proposals and European solutions directory can be found at eurostack.eu and euro-stack.com.
This blog was authored primarily by Mark Neufurth of IONOS and Stefane Fermigier of Abilian.